Vulnerability Response Process
Sungrow attaches great importance to vulnerability management throughout the product lifecycle. In compliance with standards including ISO/IEC 30111 and ISO/IEC 29147, the company has established a complete vulnerability response process to ensure effective and prompt handling of security vulnerabilities and minimize security risks.
The security vulnerability response process consists of five phases:
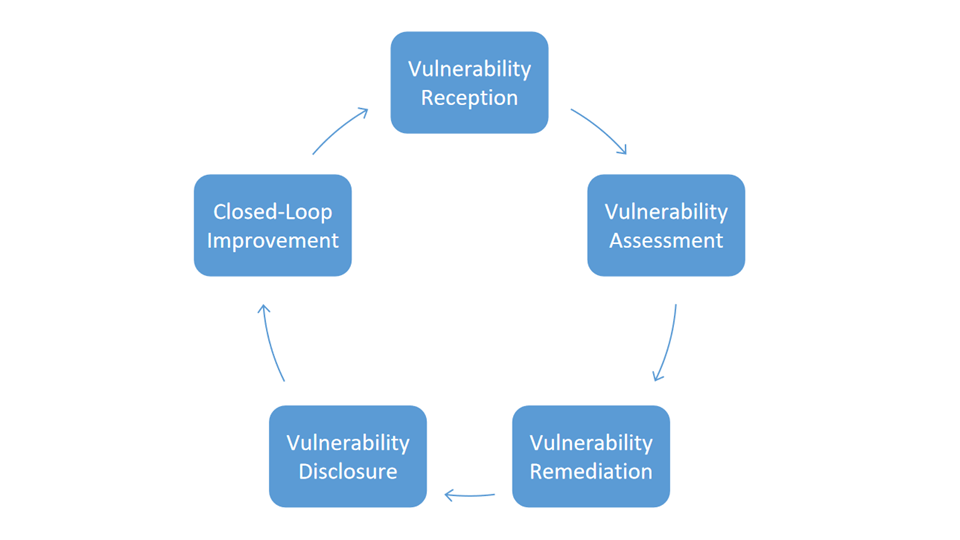
1. Vulnerability Reception
Receipt of security vulnerabilities submitted by relevant stakeholders. Sungrow encourages security professionals and industry organizations worldwide to report security vulnerabilities in Sungrow products. Meanwhile, the Sungrow PSIRT (Product Security Incident Response Team) proactively collects threat intelligence released by the industry and screens valid vulnerability information.
2. Vulnerability Assessment
Vulnerability verification, impact analysis and risk evaluation. The PSIRT analyzes and verifies security vulnerabilities, grades and scores them in accordance with the CVSS (Common Vulnerability Scoring System) standard. Relevant security experts review and confirm the assessment results to determine the final outcome.
3. Vulnerability Remediation
Upon confirmation of affected products, provide mitigation measures and solutions. For confirmed security vulnerabilities, the Sungrow PSIRT works jointly with product teams to develop, implement and deliver remediation solutions (including mitigation measures and permanent fixes), effectively addressing security risks and protecting the security and stability of customer data and systems.
4. Vulnerability Disclosure
Maintain communication with vulnerability reporters and affected customers, assist customers in vulnerability remediation, and complete coordinated vulnerability disclosure. Throughout the vulnerability response process, Sungrow keeps customers and relevant stakeholders informed of progress, assists customers in remediating vulnerabilities at the earliest opportunity, and completes coordinated vulnerability disclosure.
5. Closed-Loop Improvement
Summarize and improve from management and technical perspectives to enhance the efficiency and quality of vulnerability handling. For every security vulnerability, Sungrow conducts root-cause analysis from management and technical dimensions, summarizes lessons learned, continuously optimizes the vulnerability response process, improves inherent product security, and delivers secure and trustworthy products and services to customers.
Vulnerability Disclosure Policy
Sungrow discloses vulnerability information and remediation solutions through the following channels:
Security Advisory
Security advisory include details such as vulnerability severity, affected products and versions, impact, as well as mitigation and remediation measures. They are typically used to disclose information and fixes for Critical and High-severity security vulnerabilities in Sungrow products, enabling customers to obtain vulnerability details and assess risks. Sungrow reserves the right to issue and update security advisories.
Other Provisions
1. When handling vulnerabilities, the Sungrow PSIRT strictly controls the scope of vulnerability information, which is only shared among personnel involved in vulnerability handling.
2. Sungrow PSIRT reserves the right of final interpretation of the above policy.